The FIRST Truly
KOSHER
PHONE PLANS
with Network Level
Protection

1. Order SIM Card
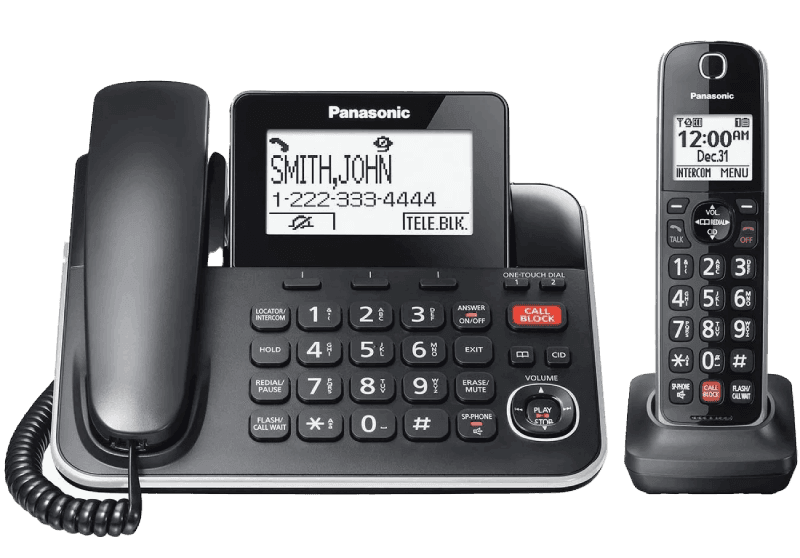
Choose your plan and
order a KOSHER SIM card.
2. Activate & Insert
Receive your pre-filtered SIM
and place it in your phone.
All plans are strictly kosher. Blocking at the network level is updated daily.
Applies to approved mobile phones only. Certain plans restrict internet access entirely. Data access is available only on approved plans and subject to kosher policy enforcement.
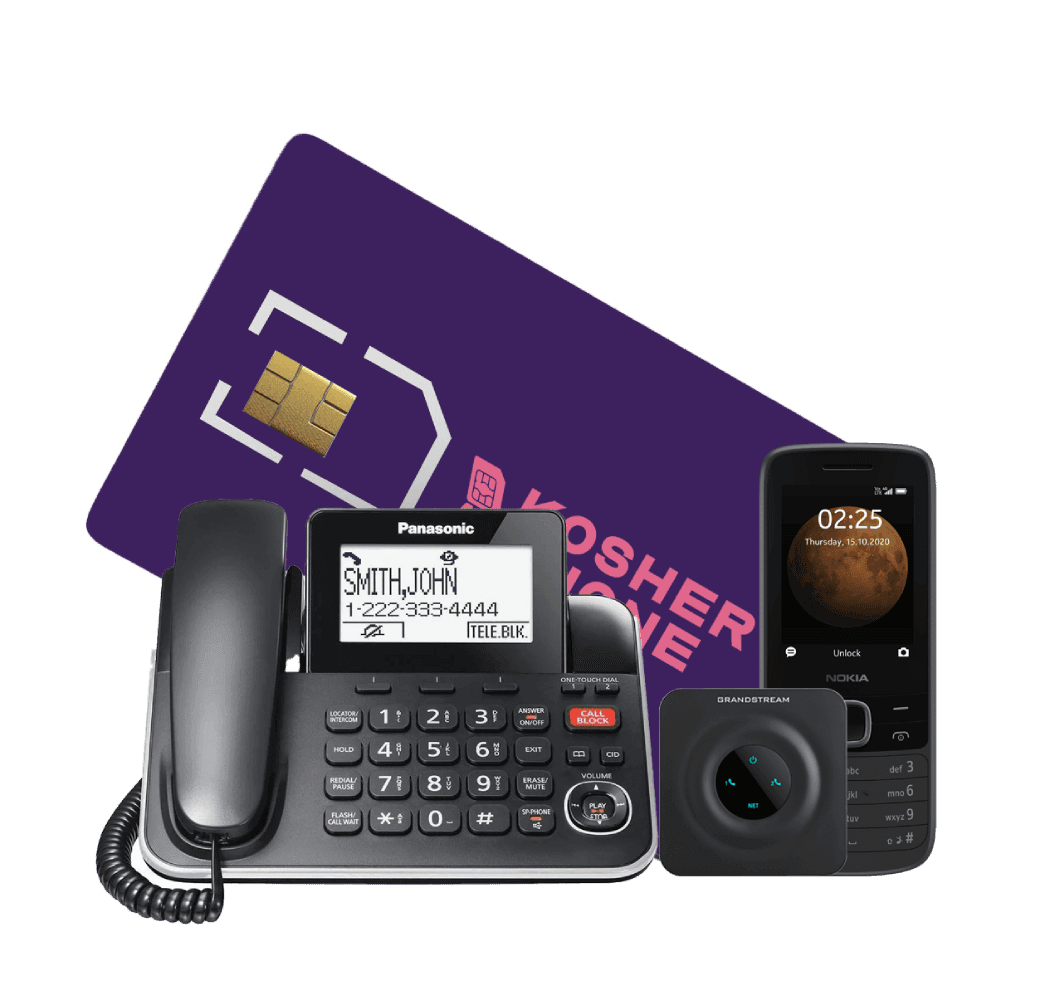
Most kosher phones focus on the device. We focus on the network. Our plans are designed to be kosher by design, not by limitation. Every plan is certified by the global kosher authority TAG and enforced directly at the carrier level.
Mobile and home phone service enforced at the network level. No apps. No workarounds. Cannot be bypassed.
What Makes Kosher Phone Different?
We are the only cellular provider offering plans that are themselves kosher certified by TAG Technology Awareness Group. Not just a phone. Not just a filter. The actual cellular plan.
This means protection that a phone alone cannot provide.
Network Level Filtering
Blocking happens at the server level, not on the device.

No Apps or Workarounds
No apps to install or configure. It works right away.

Cannot Be Disabled or Removed
Kosher restrictions cannot be bypassed, even by factory reset.

Independently Certified
Certified and audited by TAG, not self-enforced.

Check your coverage now!
We are the only cellular provider offering
plans that are themselves kosher certified by (TAG) Technology Awareness Group.
Check Your Coverage
Certification and Oversight
Kosher Phone is independently certified.
Restrictions are not controlled by the customer or the carrier.
Kosher Phone operates under the supervision of the Technology Awareness Group (TAG).
TAG is a nationally recognized organization focused on technology awareness and responsible usage.

Technology Awareness Group (TAG)

Network Level Enforcement
- All restrictions are applied at the network level
- Filtering happens before calls or messages reach the device
This Means
- No device-based controls
- No apps to install
- No settings to manage
- Restrictions cannot be removed by the user

Independent Oversight
- Filtering rules are defined by TAG, not by customers
- Updates and adjustments are made as needed to maintain compliance
This Means
- Restrictions cannot be disabled
- Factory resets do not remove controls
- Device settings cannot override the network
- Approved numbers are enforced consistently
Certification is not a feature. It is the foundation of our service!
Built-In Parental Controls
Controls are enforced at the network level. There is nothing for a child to disable.
Kosher Phone operates under the supervision of the Technology Awareness Group, known as TAG. TAG is a nationally recognized organization focused on technology awareness and responsible usage.

Technology Awareness Group
(TAG).
Parents Can Control
- Approved numbers
- Who can call
- Who can text
Parents Do Not Need to Manage
- Apps
- Passwords
- Device settings
- Workarounds

Manage Settings Portal
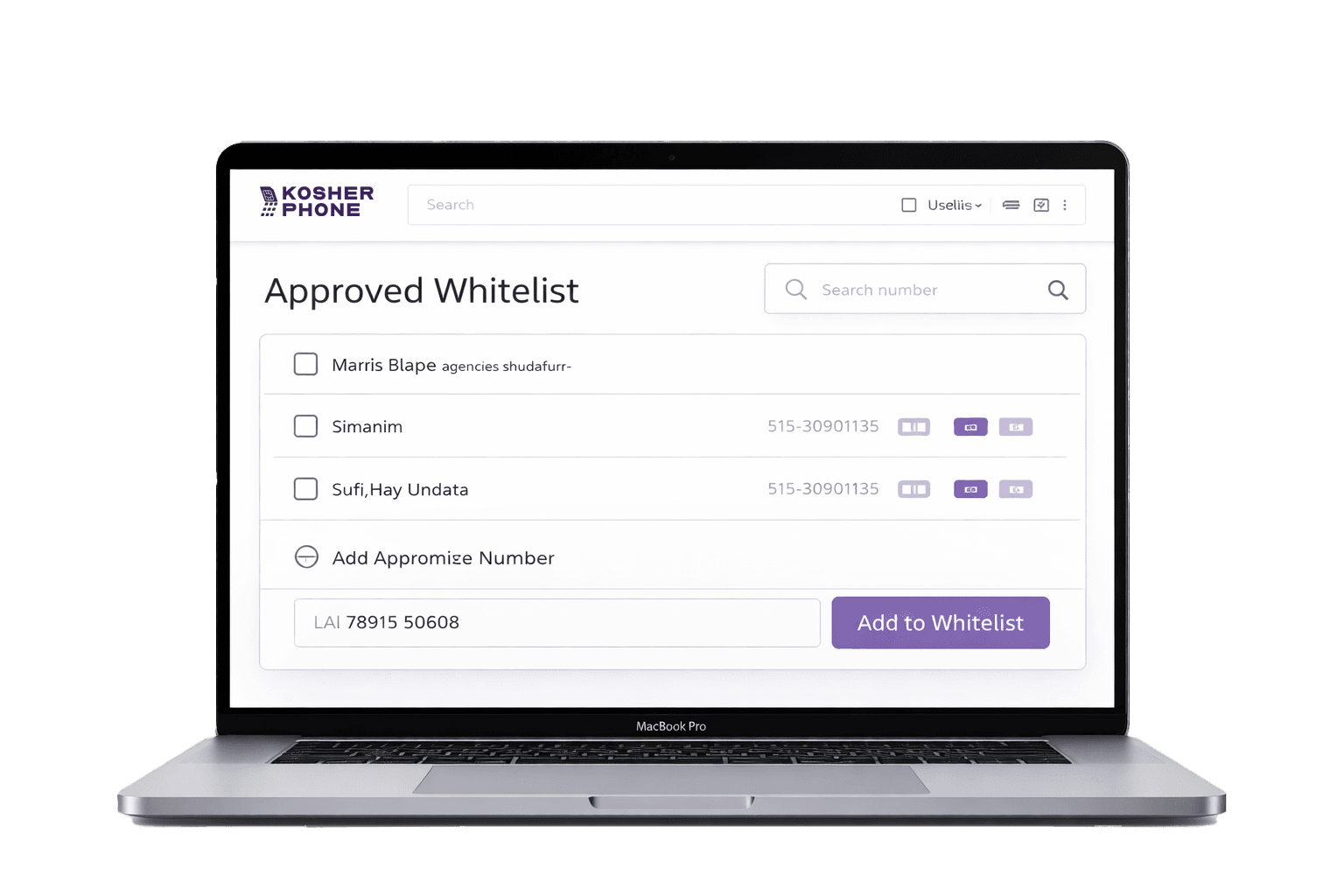
Online portal gives parents simple management tools:
- Add numbers to the base TAG safe list
- Create a custom whitelist for your child
Kosher Phone does not self-certify. Certification is independent and external.
Why This Works
No Loopholes | No Hidden Access | No Reset Tricks
ONE SET OF RULES, ENFORCED EVERYWHERE.